Establishing a Chain of Custody for Audio and Video Evidence

Closely establishing a chain of custody for digital evidence ensures its authenticity and reduces the chances of the court throwing out the data. However, differences exist with the chain of custody for digital evidence vs. physical evidence. Understanding why audio and video evidence has specific requirements will help you see why you must take extra precautions during the collection and storage of the information or seek assistance from a service that can track the chain of custody for you.
Chain of Custody Definition
A chain of custody is defined as a process that documents the recorded evidence from creation to the time it’s presented to the court. The process should include keeping the evidence recording safe, listing all persons who have handled the evidence and recording the date and time each person had the evidence for analysis, as well as their purpose and involvement with the recorded evidence.
A chain of custody must accompany media evidence submitted to the court. This chain of custody is almost always in written form. It exhibits who was responsible for the acquisition of the originally recorded evidence, who was responsible for keeping that evidence safe and who was responsible for presenting that original evidence to the trier of fact. This chain of custody includes, but is not limited to:
- Information on the original recording device, including make and model.
- Information on how the evidence was extracted from the recorder that created it.
- Digital handling information from all parties that had access to the evidence between the time of its extraction and the investigation.
Preservation of Recordings: The National Institute of Standards and Technology (NIST), Scientific Working Group on Digital Evidence (SWGDE) and Technical Working Group for the Examination of Digital Evidence (TWGEDE) guidelines describe:
- "Actions taken to secure and collect digital evidence should not affect the integrity of that evidence."
- "Persons conducting an examination of digital evidence should be trained for that Purpose."
- "Activity relating to the seizure, examination, storage or transfer of digital evidence should be documented, preserved and available for review."
When recovering evidence in the field or lab, we create a video recording of our process. This helps answer any questions about our process post-recovery. Plus, the video recording of our retrieval process effectively establishes a chain of custody.
Chain of Custody for Digital Evidence vs. Physical Evidence
Digital evidence and physical evidence must remain protected until their analysis to ensure someone has not altered them. Therefore, a chain of custody is important when handling either. However, due to the proliferation of digital media and even laypeople’s ability to alter audio, video or image files, extra care and analysis must occur when handling digital evidence.
Compared to physical pieces of evidence, digital media has three distinct differences that can affect its handling of legal cases. These differences include the following:
- Affects how law enforcement typically collects evidence
- Has a wider scope than physical evidence
- Involves both physically and personally sensitive information
Common sources of digital evidence are computers, portable electronics and the internet. However, each of these technologies presents unique concerns for forensic investigators attempting to extract information. For instance, several sites on the internet purposefully encrypt user information to hide their identities and locations. Though designed to help those under oppressive regimes connect to the internet and communicate outside the countries, others use this technology to obscure illicit online activities or searches.
Computers may temporarily store internet search information, making the examination of internet history or chats easier. Additionally, local files may contain saved footage from still or video cameras or recorded audio. Electronics, especially cellphones, present another form of digital media that can hold potential evidence. Since cellphones connect to the internet, have cameras and can record video and audio, they have several functions that overlap with computers.
Digital forensic experts use many techniques to pull data from these types of sources. The method used depends on the type of data and its storage location. Inexpert law enforcement personnel can often conduct some types of digital evidence extraction. However, when this occurs, the process should start a chain of custody that includes how the investigator pulled the information, where they pulled it from and what type of equipment was used.
The most basic method of extracting digital data involves using standard computer input devices such as a mouse, keyboard or touch screen. This manual extraction only requires a basic knowledge of operating computers.
The next level of extraction is logical. At this point, specialty equipment and knowledge of the data and system are requirements to pull the evidence successfully. Therefore, a digital forensic expert may conduct logical extraction using an external device connected to the electronic or computer.
Physical extraction uses the flash memory of a computer or electronic device. Often, experts can find recently deleted data in flash memory. Because this step requires accessing and decoding flash memory, the expert must know about reading binary and finding the needed information within the flash memory.
The most technically intensive forms of digital evidence extraction happen after pulling the computer’s memory and using special devices to read the information on it through either chip-off or micro-reading.

What Is the Importance of a Chain of Custody in Digital Media Evidence?
At the beginning of a forensic investigation, experts establish a chain of custody for audio and video evidence. Our job is to offer an authoritative analysis of electronic evidence, introduced in the form of audio or video recordings.
With the proliferation of desktop audio and video editing, recordings are frequently tampered with before they are collected as evidence. We have received recordings that have been altered and often find signs of tampering immediately.
The content of our testimony is two-fold — interpretation and authentication. We interpret scientific information for the trier of fact. We authenticate the recording as reliable evidence with integrity, and we ask ourselves a series of questions:
- Does this evidence have an established chain of custody?
- Because we recovered the recorded evidence, are we responsible for establishing the chain of custody?
- Is the recording an original or a copy?
- Has the recording been tampered with?
- Through whose hands has this recording passed before and after it was admitted into evidence?
- Where and how has it been stored?
The answers to these questions may determine the admissibility of the electronic evidence, and ultimately, whether a defendant is found guilty or innocent. Establishing and maintaining an unbroken chain of custody is vital. Without it, the evidence may be successfully challenged and ruled inadmissible no matter its probative value.
However, there are many instances when we obtain evidence from lawyers who, in turn, receive recordings from the police. If we do not retrieve the evidence personally, we must carefully read the reports, depositions and related documents that accompany the recorded evidence. This paper trail must support the construction of a timeline — an unbroken, chronological listing that accounts for the seizure, custody, transfer, storage and condition of the evidence.
As forensic experts, our job is to follow through the chain of custody and document each step.
During the collection phase, we gather the evidence. Each piece collected must undergo careful identification, recording and labeling. Throughout this phase and others, we must ensure the evidence physically stays safe and the digital information remains intact and untainted.
Next, we examine the evidence, using screenshots at every stage to document the entire process. This examination phase correlates to the analysis portion of the chain of custody. During the examination, digital media also undergoes analysis to determine if it has signs of tampering or is authentic.
The analysis is the third phase that often uses the chain of custody to inform it. For instance, if we do not collect the digital media ourselves as part of our digital forensics process, we rely on the information from the party’s chain of custody that did gather the evidence. If we see missing pieces of time in the chain of custody, we will investigate further to see if the evidence shows signs of changes.
Lastly, we create a document reporting our findings from the examination and analysis phases. This report includes a statement on the chain of custody and our methods used. We also outline the analysis methods used. Plus, our report may include any vulnerabilities or inconsistencies we find. If we suspect issues, we may recommend additional forensic analysis of the evidence or other measures to ensure the data’s authenticity.
By following these four stages and providing careful documentation the entire time, the trustworthiness of both the chain of custody and digital evidence remains intact.
Importance to the Forensic Expert of a Chain of Custody for Digital Evidence
Establishing a chain of custody is vital for court proceedings. Missing data could indicate tampering with the file, or it could happen from a problem with the software unconnected to human actions. Therefore, with a chain of custody, we can use the information to verify the data’s integrity to ensure it can be submitted in court.
For evidence experts, like our team at Primeau Forensics, the chain of custody can inform whether a piece of digital evidence with missing information experienced tampering. For instance, the chain of custody informs experts of what equipment was used to take the evidence, who created it and where it originated. Using this information and the original equipment, we can recreate an exemplar and compare it to the original file’s properties.
Significant changes could indicate an inadmissible piece of evidence someone tampered with. However, we may find that tampering likely didn’t occur and the data could provide reliable evidence.
If we find signs of tampering in the digital media, the chain of custody will help us identify who had the evidence at that point.
Importance to the Court of Establishing a Chain of Custody
A clear chain of custody can allow lawyers to successfully admit digital evidence in court without disagreement from the other side. Additionally, some experts, such as ours at Primeau Forensics, will document evidence retrieval. This extra information about handling the evidence backs up the data logged on the chain of custody, making a stronger case for the evidence as authentic and admissible.
An individual cannot create their own chain of custody in legal matters, as there is no way to back this up in court. Instead, a chain of custody must be created by authorized individuals, including people certified in evidence collection and preservation, police officers and detectives.
Expert-created chains of custody ensure the document tracing the data has followed the correct procedures and does not have timeline gaps. When combined with the expert’s analysis of the media, the chain of custody for the digital evidence has a greater role in showing the authenticity of the court’s data.
How Can the Chain of Custody Impact Your Case in Court?
When using digital evidence in court, a strong, clear timeline in the chain of custody must accompany the data. Without these components, opposition attorneys may easily challenge admission of the evidence. If the judge agrees with their argument, your evidence may get thrown out. Therefore, to ensure the admissibility of evidence into court for your case, you must have an airtight chain of custody with expert testimony and analysis to ensure the digital media’s authenticity.
The timeline must be free of any gaps or periods of time during which the exact custody and location of the evidence cannot be accounted for. A weak link in the chain of custody can easily overturn a conviction on appeal.
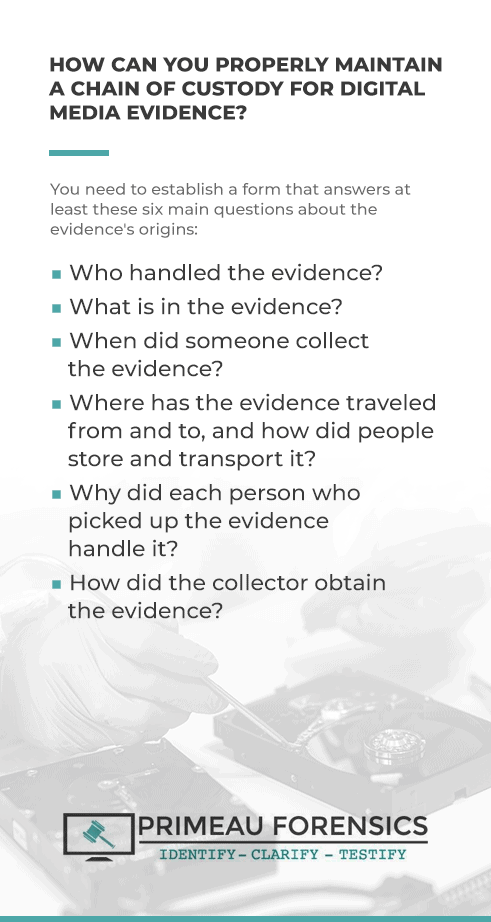
How Can You Properly Maintain a Chain of Custody for Digital Media Evidence?
Online services that track the chain of custody for electronic evidence are slowly gaining acceptance with law enforcement, security companies and the legal community. Particularly useful for the archiving and storage of video from body-worn cameras, police dash-cams and surveillance cameras — i.e., Ring and Nest — these services hope to modernize the handling of electronic evidence by eliminating the repeated transference of physical evidence, maintaining standardized security procedures and providing easy access to the content of electronic recordings.
Your chain of custody should include a form that answers at least these six main questions about the evidence’s origins:
- Who handled the evidence?
- What is in the evidence?
- When did someone collect the evidence?
- Where has the evidence traveled from and to, and how did people store and transport it?
- Why did each person who picked up the evidence handle it?
- How did the collector obtain the evidence?
Answers to these questions on a constantly updated chain of custody page will guide our forensics experts at Primeau Forensics when evaluating the evidence’s authenticity. Carefully store the chain of custody with the best evidence — an image of the hard drive — in a fireproof safe under locked, secure conditions.
When we examine digital media to create a forensic report, we use the chain of custody to inform our findings as we follow through our meticulous process of examining and analyzing digital evidence.
First, we save all packing materials to ensure the origins of the evidence we gather. Also, we carefully document the date and time when we received any evidence.
Next, we take photographs of physical evidence or screenshots of digital media.
Thirdly, we save the original piece of digital evidence. When examining digital media, it’s crucial to never use the original to avoid accidentally damaging the data. We create a clone of that file when working to preserve the integrity of the original.
Lastly, we use a hash test to verify the authenticity of our cloned file. By creating a working clone, we avoid damaging the original media as we analyze the information.
What Are the Risks of Not Having a Chain of Custody?
Failing to have an accurate chain of custody creates several hazards for the investigation, forensic expert and court case. First, not having a chain of custody puts the authenticity of the evidence into question. Without proof that no one has tampered with the evidence, investigators cannot rely on it to be accurate enough to inform their investigation.
Secondly, when turning digital media over to a forensic expert, not having a chain of custody can make the expert’s job more difficult. Unless the expert pulls the evidence themselves, they must rely on the existing chain of custody during evidence analysis. Any gaps in the chain of custody timeline could indicate tampering with the evidence, requiring the expert to further analyze it.
Lastly, inconsistencies or gaps in the chain of custody could cause the court to not accept the evidence. Or, the opposing attorneys could contest the authenticity of the evidence. If the case cannot stand without the digital evidence, the case could fail.
Contact an Expert in Collecting and Preserving Digital Media Evidence
Our services for collecting, preserving and analyzing digital media cover the range of information formats available. We offer the following types of services:
- Audio forensic services: In addition to authenticating sources, we also enhance, transcribe and compare voices on audio files.
- Forensic video analysis: Through careful analysis of the files, we can determine if a video is a copy or the original and analyze gunshots, collisions and light levels. In addition to these tasks, we can provide conversion to digital, prepare a video for trial or repair a damaged video file.
- Digital image authentication: Our digital image authentication services ensure you have the original, unedited version of a picture or digital photo. Our services are so sophisticated that 25 court cases in 10 states used our authentication services for trials.
With nearly four decades of experience, you can trust Primeau Forensics to handle your investigative needs. We’ll help you establish a chain of custody and support you during the trial. Contact us to learn more about our forensic services.
This post was last updated on December 21, 2020.
