Audio authentication is the process of forensically analyzing an audio recording to discern if it is consistent with the original events. In the technological age, audio evidence plays a significant role in court. This is mostly due to the proliferation of recorded evidence from mobile devices like the iPhone and other handheld audio recording devices. As a result, Primeau Forensics provides forensic audio authentication or forensic audio analysis services to its clients.

How Does Audio Authentication Work?
To speak directly to an expert, click below!
Authentication FAQs
- There is a glitch in my audio recording that sounds like an edit. Can you analyze my audio recording and tell me why the recording has a glitch?
A: There are many reasons an audio recording may have a glitch. It could be an error in the recording process, a bad export or corrupt file. The glitch can also be an edit where somebody removed content that was not relevant to the recording. We have all the necessary tools to run testing on the metadata, the digital back door, as well as the front door of the file itself. Critical listening and waveform analysis, as well as file sample rates that do not match the recorded sound spectrum help complete forensic audio authentication testing.
- My audio recording won’t play; can you help me get the recording to play so I can use it in a litigation?
A: There are many reasons an audio recording won’t play. This does not mean the recording is not authentic. We can begin our investigation of your audio recording with an initial review and consultation. This is a lower price point than general audio video authentication and analysis testing.
- My audio recording has a different date and time than when it was made, can you tell me if somebody altered my audio recording?
If you are looking at the MAC properties, they can be misleading as to the actual recording create date. We can bring your audio recording into the lab and determine what the actual date the recording was created on.
- I have an audio recording that was presented in a criminal case by the prosecutor, and I believe it is edited. Can Primeau Forensics help me prove it is edited?
A: Primeau Forensics is a digital media forensics lab that practices scientific best practices and unbiased testing. Our forensic authentication testing can tell if an audio recording is original and if it is not. We can also tell if a file has been converted to cover editing. After our testing process, we will notify you of the level of integrity an audio recording has.
- I have a recording in a civil litigation that has missing parts. I know because I was there when the recording was made. Can you help me determine that the recording was edited?
We are unbiased scientists who do not have a dog in the race. If your recording has been altered, we will be able to scientifically prove it. We work with attorneys to help strategically plan the reporting of our findings and testifying in court if necessary.
Submitted Successfully
We will respond soon
Audio Analysis Process

Audio Authentication Assessment
Experts will evaluate the request and review the audio file to determine if sufficient information is present to proceed with a forensic audio authentication investigation.

Critical Listening
When we first receive an audio file, our audio authentication experts will review it closely. This initial listen involves noting audio behaviors such as background noises and voices. For instance, if we notice any unusual sounds or activity, we know what to pay attention to during processing.

Analyze Digital Information
The metadata — the information embedded in the file — can make critical statements about an audio clip's authenticity. Notably, metadata will reveal the use of any third-party recording and editing software, such as Adobe Audition. This information doesn't confirm editing, but it can be a strong indicator.
Create Sample Recording
The final stage of integrity testing involves creating another recording with the same method used to create the evidence. Our audio authentication experts will try to recreate recording conditions as closely as possible to the original file. From here, we can compare hexadecimal (HEX) information and metadata to see if they match.

Edit Detection
After analyzing the metadata, we'll examine the audio itself to detect any edited audio. Tampering may involve removing sounds or even rearranging sentence structures to change the value of the information.
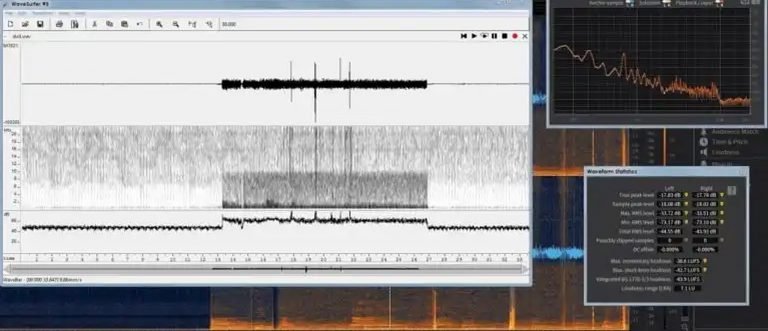
Time & Frequency Domain Analysis
Experts will measure and listen for frequency shifts in background noise, voices and other notable sounds on the recording. The forensic audio analysis investigation can determine if a recording has been laundered through a recorder, or was originally created with the alleged original device.

Document & Reporting
Compile all substantial evidence and present it as a report in preparation for courtroom use. Reports are peer reviewed internally or externally to verify the methodology applied as well as expert conclusions. This strengthens the admissibility of expert conclusions and the results from the investigation.

STATE | FEDERAL | INTERNATIONAL
After 35+ years in business testifying as a forensic audio analysis expert, Edward Primeau, our lead forensics expert, has worked with and learned from some of the greatest trial lawyers in the world. This experience has strengthened Primeau Forensics’ expert witness performance in the court room. We apply peer reviewed methodology in order to authenticate audio evidence with accuracy. We have testified in local, state and federal courts all over the United States and have extensive experience helping legal teams develop a solid trial strategy. Click HERE to read what some of them have said.